welcome
|
||||||||||||||||||||||||||||||||||||||||||||||||||||
TOTAL POPULATION CONTROL **Please Give Page Time To
Load** Mastering The Human Domain
A closer look at the upcoming Jade Helm military exercise, specifically its “master the human domain” motto, reveals a larger agenda in regards to domestic policy. In current military terminology, the “human domain” or “human domain analytics” refers to the “global understanding of anything associated with people.” Breaking down into four specific categories, mastery of the human domain results from obtaining total information awareness on a mass scale. (Shown Above) “The importance of understanding the Human Domain has increased significantly over the past decade and a half,” writes the US Geospatial Intelligence Foundation. “There has been a shift from concentration on Nation-States, to smaller organizations, to individuals.” ...With modern technological advancements allowing anyone “with a video camera and a laptop computer” to have “worldwide impact,” the federal government has not only hyper-incentivized the collection of data, but the merging of all relevant agencies. ...“They’re building an infrastructure of tyranny,” stated Infowars David Knight. “There’s a legal infrastructure with things like the NDAA, there’s a technical infrastructure with things like the capability to do dragnet surveillance, and then of course there is going to be a military and law enforcement infrastructure, and those are merging.”
...“From the very beginning this has been the NSA, the U.S. Geological Service, law enforcement, military, working to put together all this information…” David Knight said. As information from low level surveillance technologies such as Stingrays and predictive policing programs gets siphoned up to NSA data centers, a detailed global map will continue to grow with near-endless stats on all individuals. ...As Infowars has argued for weeks, Jade Helm will not result in martial law, but will move Americans one step closer to the larger agenda of total domination by the surveillance state and military industrial complex. http://www.infowars.com/master-the-human-domain-the-domestic-plan-behind-jade-helm/
Synopsis
Full Presentation
5G KILL
GRID!!
More Here: SYRIA , FALSE LEFT/RIGHT PARADIGM , SUBVERSION
TRUMP
INFRASTRUCTURE PLAN: grindall61 Twitter: https://twitter.com/grindall61 | Facebook: https://www.facebook.com/RealGrindall... | Bitchute: https://www.bitchute.com/channel/grin... | Minds: https://www.minds.com/grindall61 | Bitcoin: 142311Dsduj2pkfPs5dSFM4zo6vS3BysvZ | Go Fund Me: https://www.gofundme.com/2js4cyc | Amazon Wishlist: https://www.amazon.com/gp/registry/wi... | PO Box 523 West Covina 91793
“The 5G Rollout is Absolutely Insane.” Dr. Martin Pall, Professor Emeritus of Biochemistry and Basic Medical Sciences, Washington State University. Donald Trump’s total disregard for humanity, fauna, flora, environment – and indeed a towering ignorance – is perhaps encapsulated in recent Tweets:
Electromagnetic Sense Ireland (1) has possibly the most comprehensive, accessible, expert material to be found on 5G. It makes chilling reading. “5G is the next generation of mobile and wireless technology. It is being touted as the next best thing in communications – providing faster speeds (up to 100 times) and higher capacity transmissions to carry the massive amount of data that will be generated … A dense network of antennae is needed for 5G to operate, so these will be placed on thousands of lamp posts, poles, under manholes, street equipment etc. “As well as 5G on earth, there are plans to put 20,000 satellites in space. The intention of this is to completely cover the earth in wireless radiation. “5G will substantially increase exposure to radio–frequency electromagnetic fields RF-EMF, that has already been proven to be harmful for humans, animals and the environment.” Risks from 5G include: - Damage to the eyes – cataracts, retinal damage “The plans to beam highly penetrative 5G milliwave radiation at us from space must surely be one of the greatest follies ever conceived by mankind. There will be nowhere safe to live”, states Olga Sheean, former World Health Organisation employee and author of “No Safe Place.” “It would irradiate everyone, including the most vulnerable to harm from radiofrequency radiation: pregnant women, unborn children, young children, teenagers, men of reproductive age, the elderly, the disabled, and the chronically ill” states Ronald Powell, with a PhD, in Applied Physics from Harvard University. One hundred and eighty doctors and scientists from thirty six countries have already written to the European Union demanding a moratorium on 5G implementation. 5G is part of a seven Trillion Dollar business. So in Trump Land, clearly to hell with all life on earth – or is he actually unaware of the unimaginable horror of what he is championing? Radiation from whatever source kills, deforms, attacking the unborn, wreaks havoc – as the haunting birth deformities and cancers, environmental devastation from Hiroshima and Nagasaki, to the testing grounds of the Pacific Islands, to Iraq and the Middle East show in horrors which follow the generations. As Professor Michel Chossudovsky comments succinctly of 5G: “It’s a bit like nuclear war, it kills.” Note to readers: please click the share buttons below. Forward this article to your email lists. Crosspost on your blog site, internet forums. etc. Note 1. https://es-ireland.com/5g-5th-generation-greater-dangers/
Truthstream Media
Michgan Safe Technology SB 637 and SB 894, industry-sponsored 5G wireless infrastructure legislation passed though the Michigan House Energy Policy Committee this week with a vote of 15 to 4. "Wireless radiation has biological effects. Period. This is no longer a subject for debate when
you look at PubMed and the peer-review literature. These effects are seen in all life forms; plants, animals,
insects, microbes. In humans we have clear evidence of cancer now; there is no question. We have evidence of DNA
damage, cardiomyopathy, which is the precursor of congestive heart failure, neuropsychiatric effects... 5G is an
untested application of a technology that we know is harmful; we know it from the science. In academics this is
called human subjects research." ~ Dr. Sharon Goldberg, But 15 Michigan legislators voted to SUPPORT these bills. Do they realize they are SUPPORTING the FCC's preemption order to take power away from municipalities? Are the Michigan supporters of these bills now working for the FCC? For more information see: MichiganSafeTechnology.com
[A-MUST-SEE] Josh del Sol This is thanks to longtime UN staff member and whistle-blower Claire Edwards, who recently contacted me with this powerful story which touches all of humanity and our shared future. It is time we do what we are here to do. -Josh del Sol Beaulieu Read Claire's powerful disclosure & full story:
The Infrastructure Angle "...We need to get on this you know, figure this out before they actually slam the door on us." Patrick Wood, Video: How Technocracy ENSLAVED The World - The Real Deep State Links: C.F.R. , Bilderberg Group
Some Resources: https://emfscientist.org/ http://www.technocracyrising.com/
How Technocracy (Excerpt From Video)
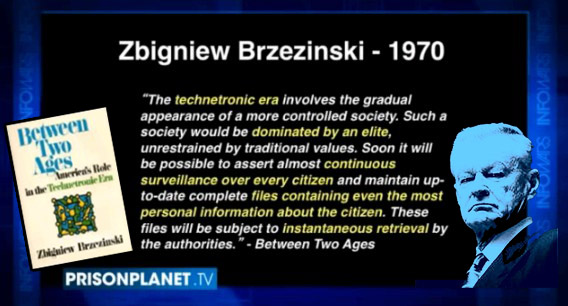
Technocracy In America: The Rise of the Info-StateIn January 2017, leading globalist scholar Dr. Parag Khanna published a book, Technocracy in America: Rise of the Info-State, that emphatically declares America’s need for a ‘direct Technocracy’. Among other things, he calls for the abandonment of the Senate and for the Supreme Court to directly modify the Constitution as it sees fit. Khanna believes in a borderless world where global Smart Cities and mega-regions will be connected to create a global society, or a giant city-state. https://www.technocracy.news/quick-start/ Patrick Wood "...All The Trilateral companies that were
associated at that time with the Trilateral Commission, they made a stampede rush to China to build infrastructure
in China. They built the highways, they built the bridges, they built the dams, they built all the stuff that you
need to do business if you will. They were the ones that set up China. Lo and behold, by the year 2000 came along
at least, Time magazine wrote an article that pointed out that China was a Technocracy. And okay, now how did that
happen? Well Brzezinski - clearly in my mind as you look back on it, a little forensic analysis - Brzezinski
purposely brought China in as a model of Technocracy...So they converted China over the couple decades into a
Technocracy. And even today China is acting like a Technocracy: not a communist dictatorship. Very few people have
picked up on this. But this is important to notice because what's happened to American manufacturing jobs?...It was
a purposeful thing to set China up to suck America dry...We've seen this happen time and time again, a certain
privacy invading technology gets invented in America. It's illegal to do it in America. There's laws against it,
they can't exercise that sort of stuff. So, these supposedly quote unquote American companies, they sneak over to
China where it's perfectly legal and they welcome them with open arms. They go over there and they prove their
technology - their spying, surveillance, whatever technology. And when they get it all done on the Chinese people,
then they just you know find ways to sneak it back into the United States to start applying it here. But they
couldn't do the testing here. So they test it over there and prove it, and then they brought it back and now we're
getting it, and they keep shoving it down our throat..."
- Patrick Wood, Video: How Technocracy ENSLAVED The World - The Real Deep State -
China and the New World Order corbettreport SHOW NOTES AND MP3: http://www.corbettreport.com/?p=12816 Military tensions, cyber espionage accusations, a brewing currency war; with every passing day,
the headlines paint a convincing portrait of an emerging cold war between China and the West. But is this surface
level reality the whole picture, or is there a deeper level to this conflict? Is China an opponent to the New World
Order global governmental system or a witting collaborator with it? Join us in this in-depth edition of The Corbett
Report podcast as we explore China's position Whitney is joined by James Corbett of the Corbett Report to discuss the overlap between the oligarchs of China and the United States and how the rise of China is intimately tied to Wall Street and Globalism. Published on 09/28/21. SHOW NOTES
More Here: General Summary/Crash Course , Full Spectrum Dominance , Wall Street
How Technocracy ENSLAVED The
World
A CONTROLLED SOCIETY DOMINATED BY AN ELITE
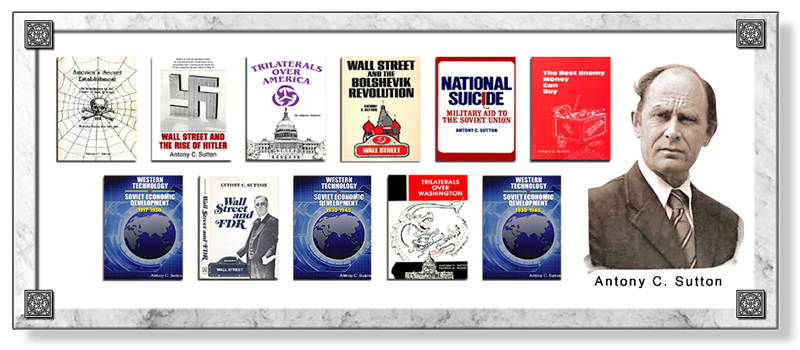
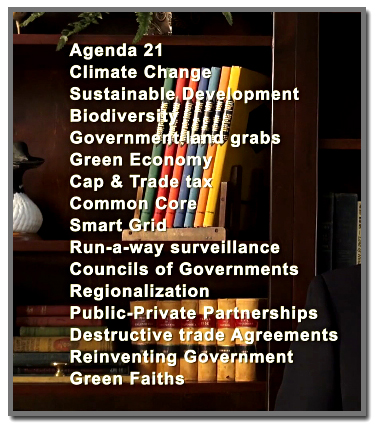
***BACKGROUND REFERENCE*** Technocracy is a replacement economic system for Capitalism and Free Enterprise, and is represented by the United Nations’ program for Sustainable Development and “Green Economy.” It proposes that all means of production and consumption would be controlled by an elite group of scientists and engineers (technocrats) for the good of mankind. Technocracy was originally architected in the 1930s but regained favor when adopted by the Trilateral Commission in 1973, under their “New International Economic Order” program. https://www.technocracy.news/faq-2/
The Roots of Technocracy with Expert Patrick M. Wood Alex welcomes to the broadcast The August Forecast & Review Editor Patrick M. Wood to discuss
how the global elite within the Trilateral Commission are replacing capitalism with their own technocracy in
order to create Technocracy Rising Contents
Exposing the Dark Agenda Behind the "Resource-Based Economy" Published on May 28, 2015 SHOW NOTES AND MP3: https://www.corbettreport.com/?p=14902 24/7 surveillance. Smart grid controls. Carbon rationing. Today we talk to
"Technocracy Rising" author Patrick Wood about the hidden history of technocracy, the dark plan for a
resource-based economy that is being pushed by the Trilateral Commission, the UN, and other globalist institutions
in order to bring about a completely managed,
SHOW NOTES: Technocracy Study Course Unabridged Figueres: First time the world economy is transformed intentionally Economic Calculation in the Socialist Commonwealth Every adult in Britain should be forced to carry ‘carbon ration cards’, say MPs
LINKS: Economy Destroyed By Design! | Transhumanism And The Technocratic Era | Educational System Dismantlement | AGENDA 21 Cliven Bundy Case Example | International Monetary Fund | World Trade Organization | BANKS RULE THE WORLD | AGENDA 21 | Climate Change | Climategate Is Still the Issue | Religious Leaders Politicians Sellout to Rockefeller Foundation
"Total control over the economic process depends directly upon total information awareness within that economic system! And now you know why they need: A Total Surveillance Society" -- Patrick Wood --
The 5G Dragnet corbettreport TRANSCRIPT AND SOURCES: https://www.corbettreport.com/5g/ Telecom companies are currently scrambling to implement fifth-generation cellular network technology. But the world of 5G is a world where all objects are wired and constantly communicating data to one another. The dark truth is that the development of 5G networks and the various networked products that they will give rise to in the global smart city infrastructure, represent the greatest threat to freedom in the history of humanity.
The Information-Industrial Complex corbettreport Half a century ago, outgoing President Dwight D. Eisenhower coined the term "military-industrial
complex" to describe the fascistic collusion between the Pentagon and America's burgeoning armaments industry. But
in our day and age we are witnessing the rise of a new collusion, one between the Pentagon and the tech industry
that it helped to seed, that is committed to waging a covert war against people the world over. Now, in the 21st
century, it is time to give this new threat a name: the information-industrial complex. Link: Transhumanism And The Technocratic Era
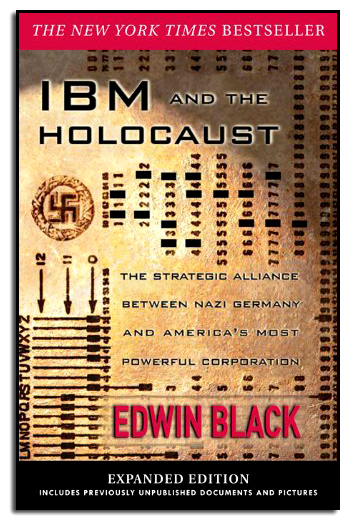
IBM and the Holocaust is the stunning story of IBM's strategic alliance with Nazi Germany -- beginning in 1933 in the first weeks that Hitler came to power and continuing well into World War II. As the Third Reich embarked upon its plan of conquest and genocide, IBM and its subsidiaries helped create enabling technologies, step-by-step, from the identification and cataloging programs of the 1930s to the selections of the 1940s. Only after Jews were identified -- a massive and complex task that Hitler wanted done immediately -- could they be targeted for efficient asset confiscation, ghettoization, deportation, enslaved labor, and, ultimately, annihilation. It was a cross-tabulation and organizational challenge so monumental, it called for a computer. Of course, in the 1930s no computer existed. But IBM's Hollerith punch card technology did exist. Aided by the company's custom-designed and constantly updated Hollerith systems, Hitler was able to automate his persecution of the Jews. Historians have always been amazed at the speed and accuracy with which the Nazis were able to identify and locate European Jewry. Until now, the pieces of this puzzle have never been fully assembled. The fact is, IBM technology was used to organize nearly everything in Germany and then Nazi Europe, from the identification of the Jews in censuses, registrations, and ancestral tracing programs to the running of railroads and organizing of concentration camp slave labor. IBM and its German subsidiary custom-designed complex solutions, one by one, anticipating the Reich's needs. They did not merely sell the machines and walk away. Instead, IBM leased these machines for high fees and became the sole source of the billions of punch cards Hitler needed. IBM and the Holocaust takes you through the carefully crafted corporate collusion with the Third Reich, as well as the structured deniability of oral agreements, undated letters, and the Geneva intermediaries -- all undertaken as the newspapers blazed with accounts of persecution and destruction. Just as compelling is the human drama of one of our century's greatest minds, IBM founder Thomas Watson, who cooperated with the Nazis for the sake of profit. Only with IBM's technologic assistance was Hitler able to achieve the staggering numbers of the Holocaust. Edwin Black has now uncovered one of the last great mysteries of Germany's war against the Jews -- how did Hitler get the names?
http://www.ibmandtheholocaust.com/
Bilderberg and the Digital New World Order Truthstream Media Please help support us on Patreon, read our goals here: https://www.patreon.com/truthstreammedia Truthstream Can Be Found Here: Link: Bilderberg Group
The Secrets of Silicon Valley: corbettreport TRANSCRIPT AND SOURCES: https://www.corbettreport.com/silicon... Once a sleepy farming region, Silicon Valley is now the hub of a global industry that is transforming the economy, shaping our political discourse, and changing the very nature of our society. So what happened? How did this remarkable change take place? Why is this area the epicenter of this transformation? Discover the dark secrets behind the real history of Silicon Valley and the Big Tech giants in this important edition of The Corbett Report.
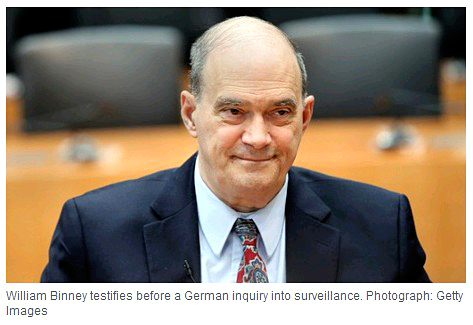
The Ultimate Goal Of The NSA Is Total Population Control At least 80% of all audio calls, not just metadata, are
recorded and stored in the US, says whistleblower William Binney
William Binney is one of the highest-level whistleblowers to ever emerge from the NSA. He was a leading code-breaker against the Soviet Union during the Cold War but resigned soon after September 11, disgusted by Washington’s move towards mass surveillance.
“At least 80% of fibre-optic cables globally go via the US”, Binney said. “This is no accident and allows the US to view all communication coming in. At least 80% of all audio calls, not just metadata, are recorded and stored in the US. The NSA lies about what it stores.” The NSA will soon be able to collect 966 exabytes a year, the total of internet traffic annually. Former Google head Eric Schmidt once argued that the entire amount of knowledge from the beginning of humankind until 2003 amount to only five exabytes. Binney, who featured in a 2012 short film by Oscar-nominated US film-maker Laura Poitras, described a future where surveillance is ubiquitous and government intrusion unlimited. “The ultimate goal of the NSA is total population control”, Binney said, “but I’m a little optimistic with some recent Supreme Court decisions, such as law enforcement mostly now needing a warrant before searching a smartphone.” He praised the revelations and bravery of former NSA contractor Edward Snowden and told me that he had indirect contact with a number of other NSA employees who felt disgusted with the agency’s work. They’re keen to speak out but fear retribution and exile, not unlike Snowden himself, who is likely to remain there for some time. Unlike Snowden, Binney didn’t take any documents with him when he left the NSA. He now says that hard evidence of illegal spying would have been invaluable. The latest Snowden leaks, featured in the Washington Post, detail private conversations of average Americans with no connection to extremism. It shows that the NSA is not just pursuing terrorism, as it claims, but ordinary citizens going about their daily communications. “The NSA is mass-collecting on everyone”, Binney said, “and it’s said to be about terrorism but inside the US it has stopped zero attacks.” The lack of official oversight is one of Binney’s key concerns, particularly of the secret Foreign Intelligence Surveillance Court (Fisa), which is held out by NSA defenders as a sign of the surveillance scheme's constitutionality. “The Fisa court has only the government’s point of view”, he argued. “There are no other views for the judges to consider. There have been at least 15-20 trillion constitutional violations for US domestic audiences and you can double that globally.”
Binney recently told the German NSA inquiry committee that his former employer had a “totalitarian mentality” that was the "greatest threat" to US society since that country’s US Civil War in the 19th century. Despite this remarkable power, Binney still mocked the NSA’s failures, including missing this year’s Russian intervention in Ukraine and the Islamic State’s take-over of Iraq. The era of mass surveillance has gone from the fringes of public debate to the mainstream, where it belongs. The Pew Research Centre released a report this month, Digital Life in 2025, that predicted worsening state control and censorship, reduced public trust, and increased commercialisation of every aspect of web culture. It’s not just internet experts warning about the internet’s colonisation by state and corporate power. One of Europe’s leading web creators, Lena Thiele, presented her stunning series Netwars in London on the threat of cyber warfare. She showed how easy it is for governments and corporations to capture our personal information without us even realising. Thiele said that the US budget for cyber security was US$67 billion in 2013 and will double by 2016. Much of this money is wasted and doesn't protect online infrastructure. This fact doesn’t worry the multinationals making a killing from the gross exaggeration of fear that permeates the public domain. Wikileaks understands this reality better than most. Founder Julian Assange and investigative editor Sarah Harrison both remain in legal limbo. I spent time with Assange in his current home at the Ecuadorian embassy in London last week, where he continues to work, release leaks, and fight various legal battles. He hopes to resolve his predicament soon. At the Centre for Investigative Journalism conference, Harrison stressed the importance of journalists who work with technologists to best report the NSA stories. “It’s no accident”, she said, “that some of the best stories on the NSA are in Germany, where there’s technical assistance from people like Jacob Appelbaum.” A core Wikileaks belief, she stressed, is releasing all documents in their entirety, something the group criticised the news site The Intercept for not doing on a recent story. “The full archive should always be published”, Harrison said. With 8m documents on its website after years of leaking, the importance of publishing and maintaining source documents for the media, general public and court cases can’t be under-estimated. “I see Wikileaks as a library”, Assange said. “We’re the librarians who can’t say no.” With evidence that there could be a second NSA leaker, the time for more aggressive reporting is now. As Binney said: “I call people who are covering up NSA crimes traitors”.
THE NSA
LINK: The NSA (National Security Agency)
SMART METERS
LINK : SMART METERS
DHS SPY GRID LINK: DHS SPY GRID
GOVERNMENT
LINK: RFID chip Mandatory at Schools
DRONES LINK: DRONES
MICROCHIP IMPLANTS
LINK: Microchip Implants
CASHLESS SOCIETY LINK: CASHLESS TRACKABLE SOCIETY
CELL PHONES ARE TRACKING DEVICES LINK: Cell Phones Are Tracking Devices
NATIONAL I.D. CARD
LINK: National I.D. Card
Pentagon Monitoring
LINK: Post Office Trucks Stasi Data Collection Nodes
[Obamacare] ...Federal Data Services Hub," which gives access to the NSA, DHS, DOJ, HHS, Social Security Administration, IRS and more LINK: Health Care
Facebook, Communications Takeover,
LINKS: Facedeals scans your face to customize deals | Communications Takeover by EAS | GOOGLE GLASS
FBI Biometric Database
LINK: India Biometrics 1.2 Billion People
BIG BROTHER LINK: Big Brother/Sis And Surveillance Systems
Big Brother in Little China corbettreport
Story #1: Big Data Meets Big Brother As China Moves To Rate Its Citizens Sesame Credit: China’s Creepy New Social Engineering Experiment (Dec. 19, 2017) Black Mirror: ‘Nosedive’ It Begins: Canadian Gov Rolls Out Points To Reward Good Citizens Story #2: Civilians Can Earn Points By Helping Police Finding Stolen Cars PDF: Netherlands Future of Police Missions “Being Excited By The Neighbors Does Not Feel Good” So You’ve Decided To Boycott Google…. Fewer Cars Stolen In The Netherlands; Thefts Drop To “Historic Low” Ep. 145 - You Are Being Gamed Mobile Phone Companies Selling Your Number, Location Story #3: Phoenix 2.0: CIA To Unleash Vietnam Era Terror Campaign On Afghanistan Wikipedia: Phoenix Program The Phoenix Program: America's Use of Terror in Vietnam by Douglas Valentine Interview 1248 – Douglas Valentine on the Resurrection of the Phoenix Program You can help support our independent and non-commercial work by visiting http://CorbettReport.com/Support & http://MediaMonarchy.com/Support. Thank You.
Israel Hacking the World Know More News Know More News with Adam Green Support Know More News! Follow me on Social Media:
Know More News Know More News with Adam Green
Israel's Tech
Know More News Premiered May 22, 2019 Know More News with Adam Green https://www.KnowMoreNews.org/ Support Know More News! Paypal Donations - https://www.paypal.me/KnowMoreNews Patreon - https://www.patreon.com/AdamGreen Venmo - @Know-More-News Know More News Know More News with Adam Green Support Know More News! Paypal Donations - https://www.paypal.me/KnowMoreNews Patreon - https://www.patreon.com/AdamGreen Venmo - @Know-More-News
Know More News Guest Link: Know More News with Adam Green
Adam Green's Documentary can be seen here: Subverting The Public
LINK: INTERNET FALSE FLAGS
New Computer Will ‘Decide If You Receive Healthcare’ Computer may soon decide if some receive healthcare
IBM’s Watson computer may soon decide if some individuals receive healthcare or not. IBM, whose stock price has sunk to its lowest in four years, has recently “announced a $1 billion investment to establish the new Watson Group.” IBM’s Watson computer processes large amounts of your information to make a better decision for you. Watson is now embedded in the Department of Veteran’s Affairs Data Center in Austin, Texas to “advise doctors on treatments for post-traumatic stress disorder.” According to their press release, the technology will “transform decision making.” Or said in a different way, if you are a Veteran in need of care, IBM’s Watson will soon make the decision about your health care for you.Big Data Used Against YouIBM’s Watson can “understand and respond to Big Data.” This is a catch-all phrase that encompasses medical literature, clinical data, personal electronic records, and doctor’s personal comments on patients. For years, it has been an open secret that all of our “Big Data” has been harvested and stored without our consent. This includes every Facebook thought, phone conversation, every purchase, and even household conversations, to name a few. There is no doubt that this “Big Data” is waiting to be used towards withholding or forcing medical treatment at the stroke of a bureaucratic pen in the future. The role being given to IBM’s Watson represents the official shift to disempower the practicing medical community and accelerate the mandates of Obamacare in your individual life. You could say IBM’s Watson is “common core re-education for the mind of the medical community.” All personal medical records will be uploaded and “delivered from the cloud” according to IBM’s press release. Presumably, the same cloud computing software that was recently hacked resulting in the public release of nude celebrity photos taken from their trusted wireless devices and computers linked to the cloud. Corrupt DataRecently, Charles Seife made major headlines when he published in the Journal of the American Medical Association (JAMA) that research misconduct is often unreported in published medical studies. These are the same medical studies that the IBM’s Watson will reference to issue orders on what treatment a patient gets. In addition, the current clinical data and medical literature being used by Watson has produced a disastrous 1 in 22 veteran suicides per day, a fast approaching 1 in 2 people with cancer, and 1 in 68 children with autism in the United States. It is the insight, humanity, courage, and empathy to look for solutions outside this broken system that will lead to better ways. While using data, old and new, from a Veteran’s Affairs system that has a treacherous public record for poor quality care, limited use for cures, and a “profits-over-people” view shows further recklessness at best and perhaps a deeper agenda at play. Fool Me OnceFrom the get go, IBM’s Watson is a slap in the face to anyone paying attention. IBM cemented its corporate influence by making Hollerith, their big data punch card sorting machines for Germany during World War II in order to better locate Jewish residents when Hitler came to power. In the words of Edwin Black, author of “IBM and the Holocaust: The Strategic Alliance between Nazi Germany and America’s Most Powerful Corporation:”
Black continues later in his historic analysis to state that IBM New York always understood from the outset in 1933 that they were courting and doing business with the Nazi party. The company leveraged its Nazi party connections to continuously enhance its business relationship with the Third Reich, Germany, and Nazi-dominated Europe. In addition, IBM and its German subsidiary Dehomag (IBM Europe) serviced the machines, including ones located in concentration camps, regularly throughout the war. Thomas A Watson, IBM’s founder, greatly admired his Nazi partners as evidence from correspondence, visits to Germany during the war, and regular gifts to Reich command. On September 11th, 1934 Watson sent the following telegram to his IBM Berlin subsidiary:
Additional Sources: Medical Research Misconduct (JAMA)
LINKS: U.S. Military Killing Its Own Troops! | Vaccines Killing Soldiers | Pawns On The Chessboard
Obama collecting personal data for a secret race database
By Paul Sperry - July 18, 2015 | 4:00pm A key part of President Obama’s legacy will be the fed’s unprecedented collection of sensitive data on Americans by race. The government is prying into our most personal information at the most local levels, all for the purpose of “racial and economic justice.” Unbeknown to most Americans, Obama’s racial bean counters are furiously mining data on their health, home loans, credit cards, places of work, neighborhoods, even how their kids are disciplined in school — all to document “inequalities” between minorities and whites. This Orwellian-style stockpile of statistics includes a vast and permanent network of discrimination databases, which Obama already is using to make “disparate impact” cases against: banks that don’t make enough prime loans to minorities; schools that suspend too many blacks; cities that don’t offer enough Section 8 and other low-income housing for minorities; and employers who turn down African-Americans for jobs due to criminal backgrounds. Big Brother Barack wants the databases operational before he leaves office, and much of the data in them will be posted online. So civil-rights attorneys and urban activist groups will be able to exploit them to show patterns
of “racial disparities” and “segregation,” even if no other evidence of discrimination exists. Housing database
The granddaddy of them all is the Affirmatively Furthering Fair Housing database, which the Department of Housing and Urban Development rolled out earlier this month to racially balance the nation, ZIP code by ZIP code. It will map every US neighborhood by four racial groups — white, Asian, black or African-American, and Hispanic/Latino — and publish “geospatial data” pinpointing racial imbalances. The agency proposes using nonwhite populations of 50% or higher as the threshold for classifying segregated areas. Federally funded cities deemed overly segregated will be pressured to change their zoning laws to allow construction of more subsidized housing in affluent areas in the suburbs, and relocate inner-city minorities to those predominantly white areas. HUD’s maps, which use dots to show the racial distribution or density in residential areas, will be used to select affordable-housing sites. HUD plans to drill down to an even more granular level, detailing the proximity of black residents to transportation sites, good schools, parks and even supermarkets. If the agency’s social engineers rule the distance between blacks and these suburban “amenities” is too far, municipalities must find ways to close the gap or forfeit federal grant money and face possible lawsuits for housing discrimination. Civil-rights groups will have access to the agency’s sophisticated mapping software, and will participate in city plans to re-engineer neighborhoods under new community outreach requirements. “By opening this data to everybody, everyone in a community can weigh in,” Obama said. “If you want affordable housing nearby, now you’ll have the data you need to make your case.”
Mortgage database
Meanwhile, the Federal Housing Finance Agency, headed by former Congressional Black Caucus leader Mel Watt, is building its own database for racially balancing home loans. The so-called National Mortgage Database Project will compile 16 years of lending data, broken down by race, and hold everything from individual credit scores and employment records. Mortgage contracts won’t be the only financial records vacuumed up by the database. According to federal documents, the repository will include “all credit lines,” from credit cards to student loans to car loans — anything reported to credit bureaus. This is even more information than the IRS collects. The FHFA will also pry into your personal assets and debts and whether you have any bankruptcies. The agency even wants to know the square footage and lot size of your home, as well as your interest rate. FHFA will share the info with Obama’s brainchild, the Consumer Financial Protection Bureau, which acts more like a civil-rights agency, aggressively investigating lenders for racial bias. The FHFA has offered no clear explanation as to why the government wants to sweep up so much sensitive information on Americans, other than stating it’s for “research” and “policymaking.” However, CFPB Director Richard Cordray was more forthcoming, explaining in a recent talk to the radical California-based Greenlining Institute: “We will be better able to identify possible discriminatory lending patterns.”
Credit database
CFPB is separately amassing a database to monitor ordinary citizens’ credit-card transactions. It hopes to vacuum up some 900 million credit-card accounts — all sorted by race — representing roughly 85% of the US credit-card market. Why? To sniff out “disparities” in interest rates, charge-offs and collections.
Employment database
CFPB also just finalized a rule requiring all regulated banks to report data on minority hiring to an Office of Minority and Women Inclusion. It will collect reams of employment data, broken down by race, to police diversity on Wall Street as part of yet another fishing expedition.
School database
Through its mandatory Civil Rights Data Collection project, the Education Department is gathering information on student suspensions and expulsions, by race, from every public school district in the country. Districts that show disparities in discipline will be targeted for reform. Those that don’t comply will be punished. Several already have been forced to revise their discipline policies, which has led to violent disruptions in classrooms. Obama’s educrats want to know how many blacks versus whites are enrolled in gifted-and-talented and advanced placement classes. Schools that show blacks and Latinos under-enrolled in such curricula, to an undefined “statistically significant degree,” could open themselves up to investigation and lawsuits by the department’s Civil Rights Office. Count on a flood of private lawsuits to piggyback federal discrimination claims, as civil-rights lawyers use the new federal discipline data in their legal strategies against the supposedly racist US school system. Even if no one has complained about discrimination, even if there is no other evidence of racism, the numbers themselves will “prove” that things are unfair. Such databases have never before existed. Obama is presiding over the largest consolidation of personal data in US history. He is creating a diversity police state where government race cops and civil-rights lawyers will micromanage demographic outcomes in virtually every aspect of society. The first black president, quite brilliantly, has built a quasi-reparations infrastructure perpetually fed by racial data that will outlast his administration. Paul Sperry is a Hoover Institution media fellow and author of “The Great American Bank Robbery,” which exposes the racial politics behind the mortgage bust.
LINK: Divide and Conquer
Jade Helm Decoded - Revisited - Published on Jul 4, 2015 New content begins at the 9 minute 15 second mark. Read more: http://www.infowars.com/jade-helm-the...
Mastering The Human Domain Confirmed: Jade Helm Is For The American People Published on May 8, 2015 David Knight and Rob Dew break down the sinister purpose behind Operation Jade Helm detailing how it is part of a broader plan to have the military and police forces work together to control the people in times of economic crisis and natural disaster.
LINK: Fort A.P. Hill Training Center
http://geointv.com/archive/mastering-the-human-domain/
| ||||||||||||||||||||||||||||||||||||||||||||||||||||






 "
"




 On 5 July he spoke at a
On 5 July he spoke at a  A Fisa court in 2010 allowed the NSA to spy on 193 countries around the world,
plus the World Bank, though there’s
A Fisa court in 2010 allowed the NSA to spy on 193 countries around the world,
plus the World Bank, though there’s